The cyber threat landscape is growing rapidly, and organizations around the world are struggling to find the protection they need to stay outside their risk zones. Even the best antivirus applications are known to block almost half of the threats. Traditional antiviruses only look for signatures of known malware, these signatures can be easily modified or copied. Looking at the behavior of the malware, it is seen that its basic structure cannot be changed. Along with the continuous increase in attacks, new tools are constantly being developed by cyber security experts and network administrators to protect networks and take advantage of new technologies.
Dwell Time
Dwell Time is the expected time to access information. For example, when a user clicks on a link from the results of his search in the search engine, it is the time it takes to view the document. Considering the time spent by the user at this stage, short waiting times mean that the query purpose of the user viewing the result is not met. Long waiting times are a sign that the purpose of the user’s query has been completed.
Within the network, Dwell Time refers to the time an attacker can freely roam the network and access enough information without being detected. As a result of many types of research, the average Dwell Time in 2020 was analyzed as 56 days.
EDR, MDR, and XDR are tools developed to reduce this waiting time to a least, detect the attacker, and notify or prevent the attack. It ensures that the threats that may occur in the network are detected quickly and that the related output/alarm is reported to the network administrators. EDR, XDR, and MDR have many common genes, that come from the same foundation but differ in their approach to security. EDR and XDR focus on detecting and responding to threats on the network, but MDR is a service managed by a third party.
- EDR – Endpoint Detection and Response
- XDR – Extended Detection and Response
- MDR – Managed Detection and Response

EDR
EDR is a cybersecurity solution that captures the activity of user devices after they connect to the network and leverages advanced analytical monitoring to provide real-time visibility into the network. Thus, EDR focuses on threats that may come from users’ devices. It plays a role in detecting anomalous activity, endpoint threat detection, alerting the network administrator to information security, preventing the spread of attacks, and improving network health.
Working with the classification-based threat detection algorithm, EDR solutions are designed to only compare the detected threat element with before detected threats and perform an automatic action when it matches. Queries an existing database with up-to-date virus signatures to ensure security against known threats. Traditional endpoint security is reactive and detects potential security threats by matching known signatures and attack patterns. EDR, on the other hand, is predictive and focuses on identifying advanced persistent threats and never-before-seen malware designed to evade traditional security defenses. But by focusing more on active monitoring of the network, it distinguishes itself from other products that run in the IDS-IPS structure. This makes EDR technology more suitable for detecting and identifying unknown threats such as advanced persistent threats (APT – Advanced Persistent Threats). APTs, as the name suggests, are more sophisticated cyber threats that go undetected for long periods. Thus, EDR only monitors, monitors, and defines, informs the network administrator about which threats may exist at the endpoints, and ensures that the threats that may arise are resolved quickly.

The diversity of devices that allow users to connect to the network and communicate with applications, and the continuous development of different types of threats, is a factor that makes it easier for attackers to target endpoints. Thus, endpoint security is always of paramount importance to systems that detect threatening behavior before malicious action occurs.
EDR solutions record and store threatening queries, behaviors, and security events, allowing network management teams to more quickly and easily detect and analyze suspicious activity over time. In case of a breach or threat, it isolates malware. The behavior of the threat element is learned by running the isolated file in a secure environment (virtual environment). Thus, a comprehensive root cause analysis and faster response to the incident are provided by EDR.
EDR does not provide full network protection and must be used in conjunction with other cybersecurity tools. EDR can be considered an evolution of traditional antivirus software. The fact that it can be integrated with a large solution such as QRadar or SIEM gives EDR a great advantage. Additionally, when used as part of a SIEM, EDR solutions also add to a significant volume of alerts.
Modern networks have IoT devices, Firewalls, Cloud Apps, and multiple app clusters. This has led to the emergence and development of XDR technology.
XDR
Palo Alto Networks was the first company to introduce the concept of XDR with Cortex XDR in 2018. The main purpose of the company at this stage has been to provide security teams with a higher level of threat awareness and tools to eliminate vulnerabilities beyond the service that EDR technology can offer. XDR solutions recognize that endpoint threat detection alone is not sufficient to protect the network infrastructure, and therefore includes all network devices in its range of operations.
Maximum attention is required to maintain network security in a healthy way. XDR focuses on threats involving applications and critical areas, being responsible for all network security such as firewalls, IoT devices, or cloud applications. Thus, it combines many solutions used to provide protection across the entire network. With the use of XDR, threats in the network are identified and eliminated, and potential threats to businesses are destroyed before they become active. Thus, possible interruptions are prevented. In this way, it not only helps to protect the network against modern attacks but also protects against potential threats that have not yet been detected.
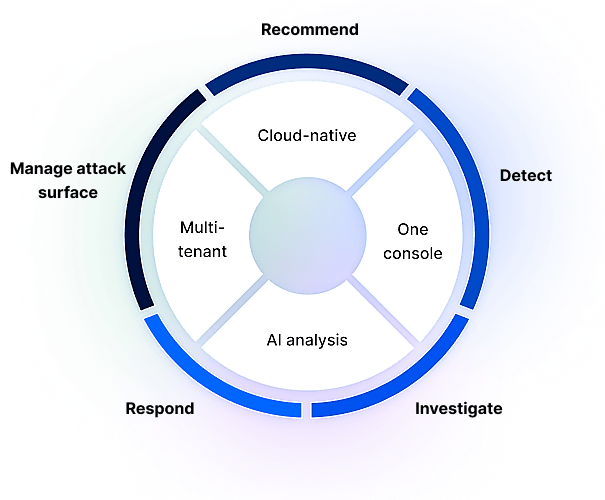
XDR has a more advanced working structure compared to other solutions. Discovered threats are categorized and sorted by priority and criticality. All threat data is centralized in a single dashboard, making it easy for teams to prioritize responses. Organizations that purchase multiple and disparate security products to create a multi-layered security architecture can create a complex security stack that generates many alerts without the appropriate context. Thanks to the high efficiency provided by the use of XDR, a lower cost and simpler network security are enabled.
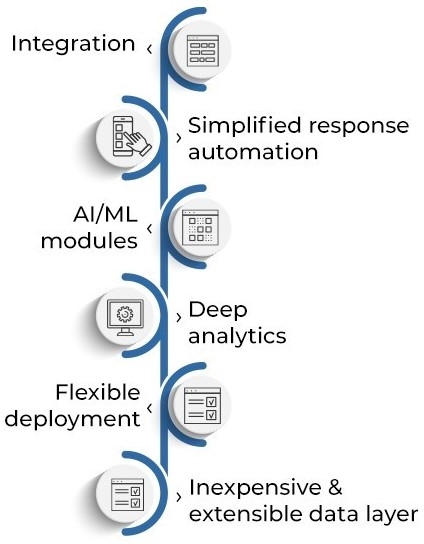
Efficiency is a fundamental principle for XDR products. Automating certain processes gives security teams high visibility and gives them time to work on other projects. Leveraging the power of artificial intelligence, machine learning, and automation, XDR periodically examines thousands of logs of information. The primary purpose of XDR technology is to provide security teams with accurate, context-rich alerts. XDR tools are designed to increase the efficiency of security operations with comprehensive automation capabilities such as monitoring anomalies, extracting information from relevant data sources, sending alerts, and even remediation. XDR is offered as a service (SaaS), making it easy for businesses to access this technology. For this reason, it is believed that the spread of XDR technology will change the structure of the security industry.
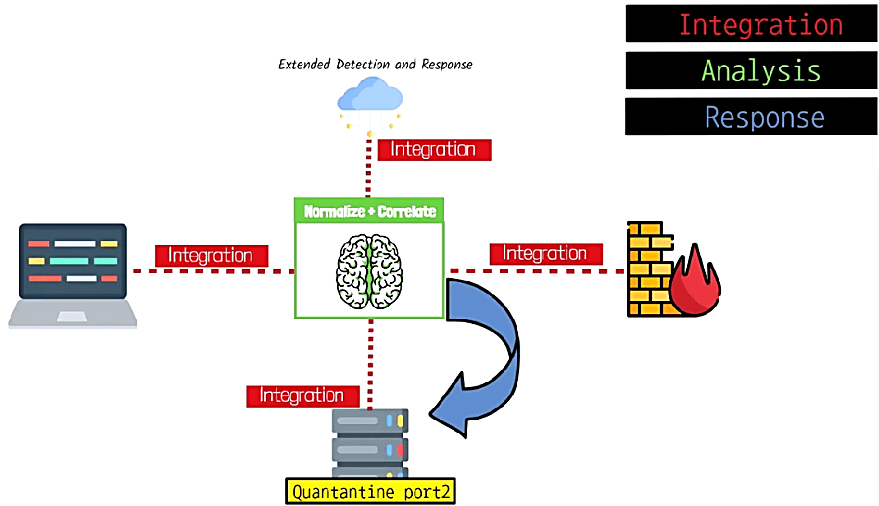
Besides, XDR pulls data from multiple security products to correlate telemetry data that would otherwise be difficult to find manually. Telemetry means remote monitoring or control of a system or facility. It has the ability to automatically or manually respond to detected threats. It can make its own decisions based on learning from the threat it detects and then responds to the relevant device to reduce the risk on the network. XDR basically consists of 3 main components; Integration, Analysis, and Response.
- Integration, is a critical component for any XDR platform. The component can receive information about the products on the network and work in line with this information. Instead of just examining telemetry data such as Syslog and SNMP, it also deepens through the API to respond when an event is detected. This means that XDR software can identify more advanced threats.
- Analysis, correlates the obtained data with all other different data types and products. This part of the process is the analysis or detection phase. Artificial intelligence software is usually used to find outliers and determine their behavior from the data received over the network. In addition, XDR calculates values for collected data in real-time, making it a faster process to identify the root cause of problems.
- Response, when the AI engine determines the threat it finds as a security risk, the response phase takes action based on the command configured by the network administrator. Thus, it can automatically correct the problem by responding to the relevant security devices. XDR tools can forward query suggestions to network administrators and advise on responding and remediating threats to assist with further investigation.
MDR
The MDR service emerged with the overwork of the cyber security teams and this work started to become insufficient and inefficient after a point. MDR only offers visibility into a single dataset, rather than examining network or cloud-based threats. MDR acts as a remote SOC providing round-the-clock access to cyber security professionals.
Because MDR is a service rather than a tool, it works differently from both EDR and XDR. While EDR and XDR are strictly focused on technology, MDR offers a different cyber security solution. MDR is a managed service that conveniently combines the benefits of EDR and XDR and helps create an in-house security program. MDR is a cyber security service typically provided by a managed security service provider (MSSP). For this reason, MDR providers state that MDR will provide additional benefits as a managed service if used in conjunction with an EDR or XDR service.
MDR is proactive and focuses on threats. MSSP, on the other hand, is designed to focus on reactive vulnerabilities. Unlike MSSP, MDR services focus on detection, response, and threat capture rather than security alert monitoring. MSSPs manage firewalls, but MDR does not provide the same level of threat research, or analytical review. MSSP services recognize security issues, but MDR services reveal the details of the threat. In most cases, however, MDR offers a service approach to traditional detection and response activities.